DISCOVERY
Discover Non-Human Identities
Get a complete and up-to-date inventory of non-human identities and AI Agents in your environments. See their associated risk, vendors, business value, and owners in one place.
PRODUCT CAPABILITIES
Continuous NHI discovery
Real‑time inventory
Automatically discover every service account, token, secret and AI Agent across SaaS, cloud, on‑prem and secret managers, updating with each provisioned or revoked identity.
Deep context & ownership
Expose shadow agents and orphaned tokens by linking each identity or agent to its human creator, vendor, environment, permissions and usage patterns.
Cross‑environment correlation
Attend to redundant connections, orphaned credentials, and blast‑radius risks through visibility into the data flows between NHIs and agents
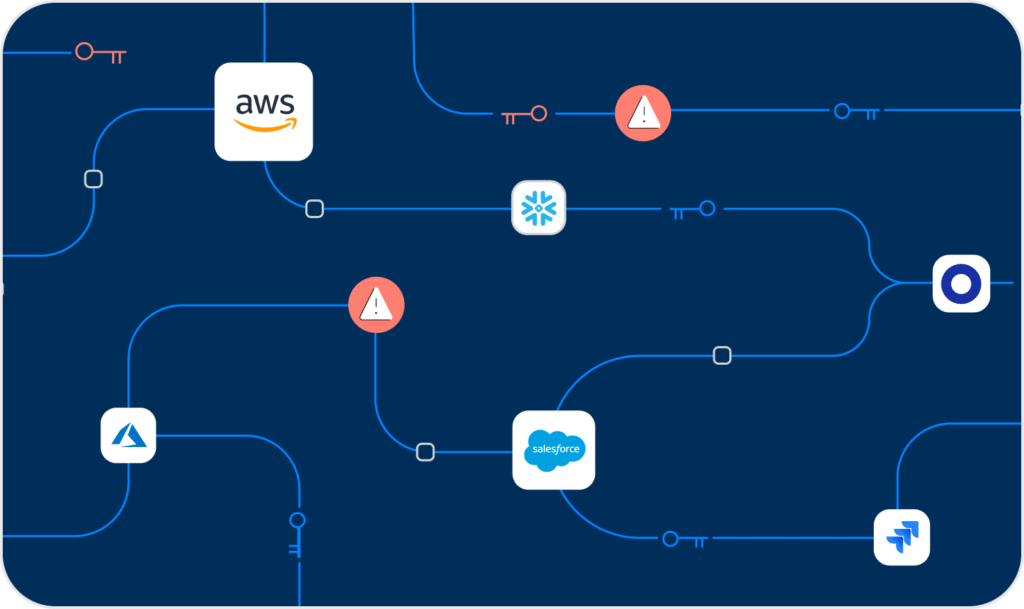
We secure NHIs across IaaS, SaaS, PaaS, and On-Prem environments
From AWS, Azure, ChatGPT, GitHub and BigQuery to Salesforce, Office365, and CoPilot, we ensure your environments are protected from NHI risks.

FEATURED
Why machine credentials are your biggest blindspot
Non-human identities are a wild west of ungoverned access. But what are they? How can you monitor them? and why should you care?