The CircleCI breach: The results of a stolen access token
Following a reported data breach last month, the company confirmed in a first comprehensive aftermath analysis that customers’ secrets and encryption keys were stolen. This breach joins a series of recent attacks using access tokens and API keys to perform privilege escalation and breach companies’ core environments (like GitHub, Google Workspace, Salesforce, Snowflake and others) to steal sensitive data such as code repositories and customer data.
The CircleCI breach started from one of the company’s engineering employees’ computer, which was compromised by malware that bypassed their antivirus solution. The compromised machine allowed the threat actors to access and steal session tokens. Stolen session tokens give threat actors the same access as the account owner, even when the accounts are protected with two factor authentication.
Since the engineering employee had privileges to generate production access tokens as part of their regular duties (like most engineers), the threat actors were able to escalate privileges in order to access and exfiltrate data from customer environment variables, tokens, and keys, all without CircleCI’s knowledge.
CircleCI reported that while customer data was encrypted at rest, the threat actors were able to obtain the encryption keys that allowed them to decrypt the customer data and potentially access encrypted customer data.
Access tokens and API keys don’t have MFA
The creation and use of access tokens and API keys is a common practice in organizations, allowing engineers and other employees to integrate apps to companies’ core systems in an effort to streamline work processes and increase productivity.
However, while user access is protected via multiple solutions (MFA, Okta etc), app2app access including access tokens and API keys (which give the exact same access as a username and password), are left unprotected by most organizations. This makes companies susceptible to data breaches just like the CircleCI exploit, the Slack breach, and even the infamous SolarWinds attack.
How to minimize the risk of a similar breach
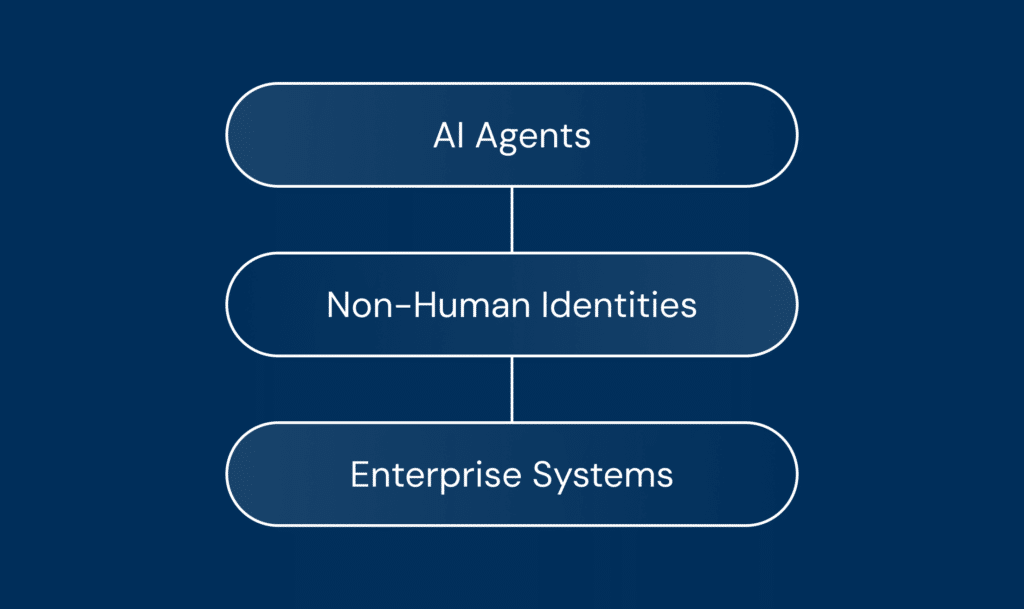
While many organizations use hundreds if not thousands of third party apps through API keys, service accounts and access tokens, very few properly secure these non-human connections that could lead to service supply chain attacks.
There are, however, a few steps you can take to minimize this unmonitored attack surface:
- Start with having a basic understanding of your existing non-human connections and decide if they are still required. If not, make sure to offboard them correctly and completely.
- Regularly inspect third party access to your critical systems, and keep privileges and exposure to the necessary minimum. That will help reduce the blast radius of potential attacks.
- Insider threats and human errors are very common, and can be critical. Always assume secrets can be compromised and rotate them as often as possible.
- Make sure you have visibility into tokens that seem to be abused and behave differently than expected.
- Utilize IP restrictions correlated to tokens provided to third-parties.
- Have an automated system in place that allows you to quickly assess your exposure and guide you on how to fix issues in case of a supplier incident such as the CircleCI one.
Support productivity and automation with Astrix
Astrix helps organizations secure app-to-app connections by monitoring and securing all the access tokens, API keys, and service accounts that create these connections, from creation to expiry. That allows organizations to ensure their core systems are securely connected to third-party applications.
Using an agentless and low friction approach, the Astrix security platform provides comprehensive visibility into all access tokens across SaaS, PaaS and IaaS environments such as Workato, Microsoft 365, Slack, Zapier and more. This allows businesses to identify third-party connections, detect risks, remediate gaps and manage the complete lifecycle of every connection to prevent new risks from arising.
With Astrix, businesses can take full advantage of the power of app-to-app automation and integration without compromising on security.
Contact us to learn more and get our security expert assistance.