Discover & Secure
Shadow AI
Astrix helps tech leaders get visibility and security
context into all GenAI access to their core
business platforms – from Salesforce and M365
to GitHub and AWS.
“Hey ChatGPT, review and optimize our source code”
“Hey Jasper.ai, generate a summary email of all our net new customers from this quarter”
“Hey Otter.ai, summarize our Zoom board meeting”
How we helped Guesty minimize Generative-AI risks
“AI is here to stay and we don’t want to block innovation. With Astrix we can safely leverage the power of AI. Astrix is a lighthouse in a sea of AI integrations.”
Gilad Solomon
Head of IT & IS
Book a 30 minutes discovery session with one of our experts:
Free – No strings attached – Agentless & zero friction
Gen-AI exposure in numbers
Mid-size organizations already have, on average, 54 Generative-AI integrations to core systems like Slack, GitHub and Google Workspace.*
*Astrix Security Research Group
Unleash the power of Generative-AI Without compromising security
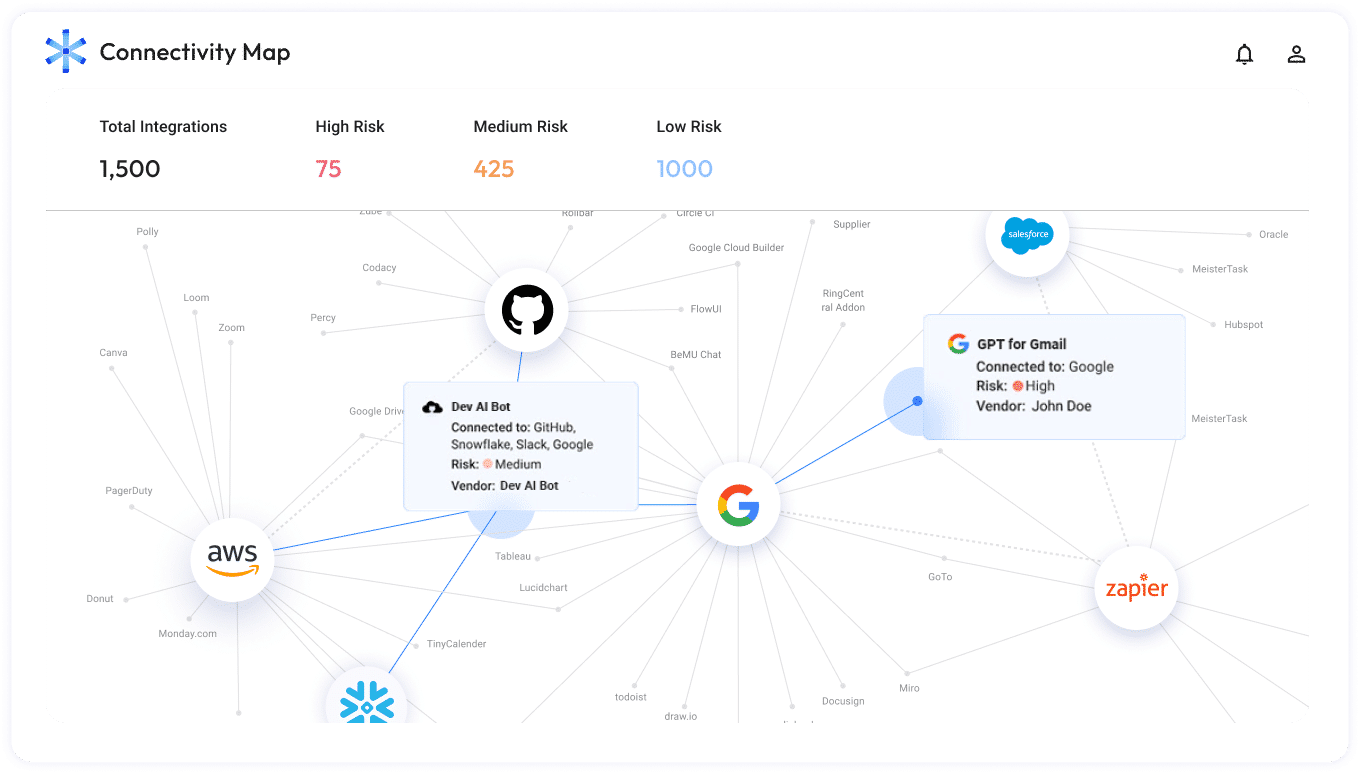
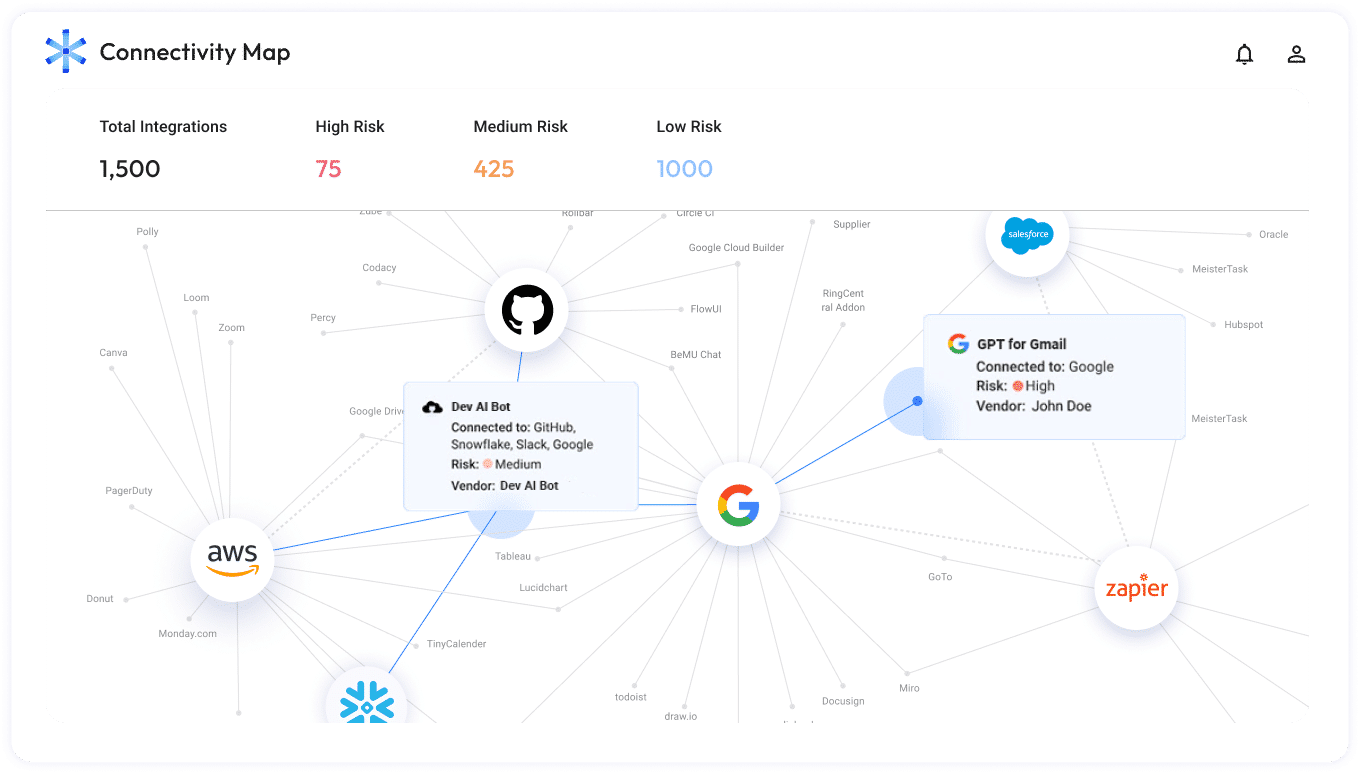
The Astrix Platform provides security teams visibility into AI third-party services your employees are connecting, as well as control over permissions and properly evaluate potential security risks.
With Astrix you get:
- Real time inventory of AI-tools in use
- Anomaly detection: stolen tokens, internal app abuse in real time
- Automated security guardrails to easily allow or disallow AI integrations
- Auto remediation workflows and allowing end-users on resolving their security issues independently.
- Reduced attack surface – remove connections with untrusted AI app vendors, over privileged access and redundant AI connections
Unleash the power of Generative-AI Without compromising security
The Astrix Platform provides security teams visibility into AI third-party services your employees are connecting, as well as control over permissions and properly evaluate potential security risks.
With Astrix you get:
- Real time inventory of AI-tools in use
- Anomaly detection: stolen tokens, internal app abuse in real time
- Automated security guardrails to easily allow or disallow AI integrations
- Auto remediation workflows and allowing end-users on resolving their security issues independently.
- Reduced attack surface – remove connections with untrusted AI app vendors, over privileged access and redundant AI connections
Trusted by industry leaders



Astrix meets the highest
industry standards