Set and enforce access policy for AI agents
Astrix now offers granular, identity-based access policies for AI agents, empowering security teams to directly control agent access permissions.
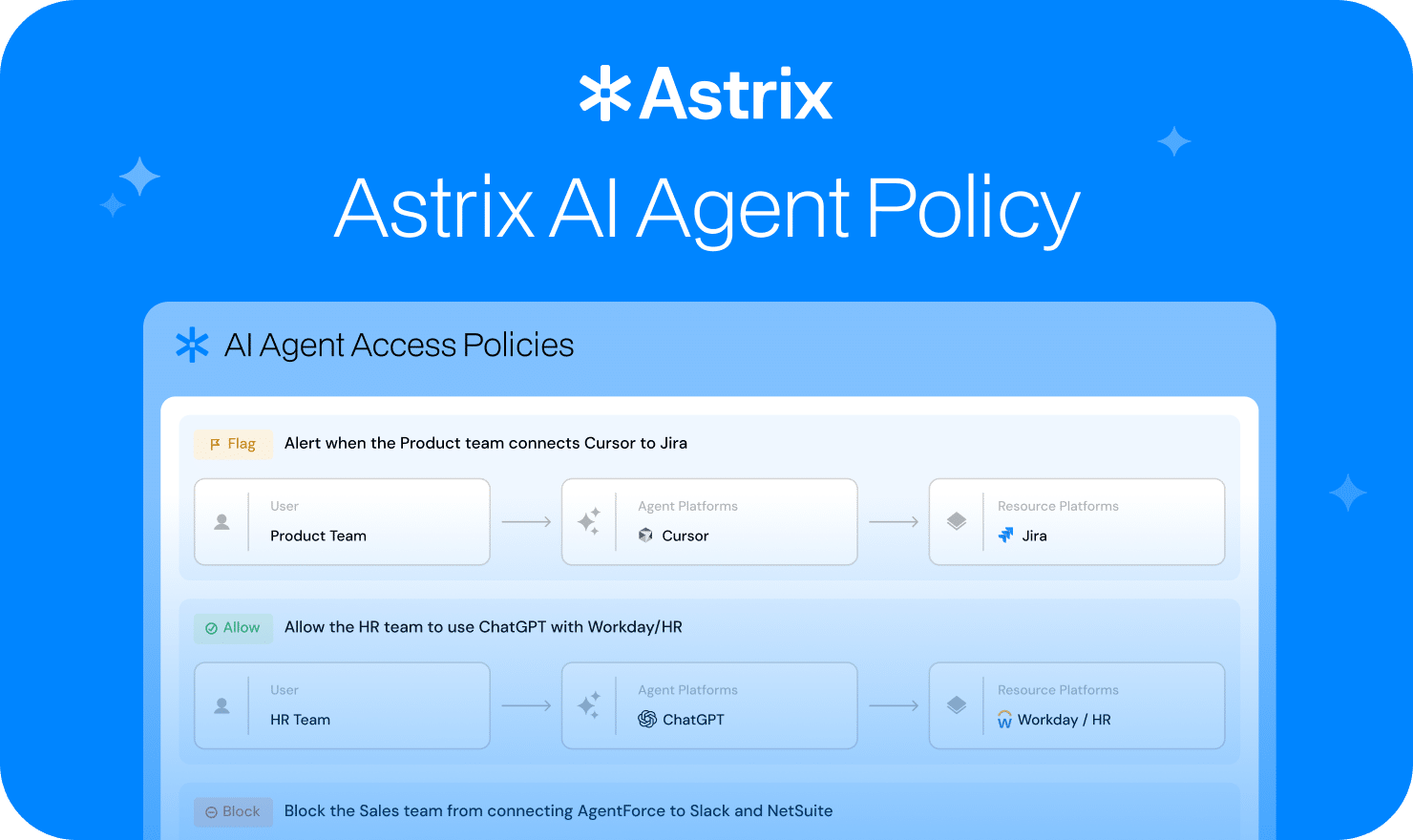
Astrix now offers granular, identity-based access policies for AI agents, empowering security teams to directly control agent access permissions. Allow, flag, and block rules can be scoped by user, department, platform, and resource type, and are evaluated before any action is executed.
Watch it in action
The best way to understand what this looks like in a real environment is to see it working. In this interactive demo, we walk through how policies are created, how they are enforced in real time inside Cursor, and how violations surface in the AI agent inventory.
The Problem: Agent visibility without control
Discovery tells you what exists. It doesn't govern what agents are allowed to do with the access they have.
An AI coding agent like Cursor runs with real credentials, against real systems. If a Sales employee has connected it to Sentry - even inadvertently - that agent can query issues, create pull requests, and read engineering data. There's no policy preventing it. The agent isn't behaving maliciously. It's behaving exactly as configured. The problem is that no one deliberately decided to grant that access.
Multiply this across the hundreds or thousands of agents now running in a typical enterprise, and the scope becomes clear. Most agent access hasn't been reviewed. Most of it has never been subject to any policy at all.
How Astrix AI agent policies Work
Astrix Agent Policies is a policy engine built into the Astrix platform. It lets security and IT teams define rules that govern what AI agents are allowed to do - scoped by who is using the agent, which platform they're using, and which resources they're trying to reach.
Every action an agent is about to take against an organizational resource triggers a real-time policy check. Astrix returns an allow, flag, or block decision before the action executes.
There are three enforcement modes:
Allow - this access is explicitly approved. The agent proceeds normally.
Flag - the access proceeds, but Astrix logs a violation and surfaces it as a finding on the agent. The agent's risk profile updates to reflect the policy breach. Your security team can review and decide what to do next.
Block - the action is stopped before it executes. The agent receives a deny response. Nothing reaches the target resource.
Policies are evaluated in priority order. The first matching policy determines the action. A default Shadow AI policy at the bottom of the list ensures that any agent activity not matched by an existing policy is automatically flagged - nothing falls through the cracks.
What an agent policy looks like in practice
A contractor's Cursor agent tries to fetch documentation from Notion. The beforeMCPExecution hook fires. Astrix checks the policy: this contractor doesn't have approved access to Notion via Cursor. The request is blocked before it leaves the machine. The contractor sees a deny message in Cursor's chat. Nothing reached Notion.
That same hook fires for a Sales employee asking Cursor to draft a customer email and save it to Notion. Notion is allowed for this user. The task completes normally. Enforcement is precise, not a kill switch.
A Sales employee's Cursor agent connects to Sentry. There's no block policy for this yet - but there's a Flag policy for Sales agents accessing engineering tools. The access proceeds. But Astrix logs a violation, surfaces it as a finding on the agent in the inventory, and elevates the agent's risk score. The security team can see it, review it, and decide whether to escalate to a Block.
The signal that matters
Policy violations don't disappear into a generic alert queue. Each one is attached directly to the agent that triggered it - named, timestamped, and linked to the exact policy that fired. Security teams can see which agent violated a policy, which resource it tried to reach, and when - without correlating across logs or dashboards.
Triage is fast. The agent is there. The finding is there. The remediation path is one step away.
Discovery and control are the foundation
A complete agent inventory and real-time policy controls are the prerequisites for AI productivity at scale. Without knowing which agents are running and what they can do, there's no basis for deciding which to trust, which to expand, or how to build on the isolated deployments already in place across the organization.
Finding every agent and controlling what each one can do: that is what a functional agent security program looks like in 2026.
If you want to see how Astrix Agent Policies would work across your own environment, book a demo today.