Lessons from the GTIG Advisory on the Salesforce OAuth Token Breach
On August 26, 2025, Google Threat Intelligence Group (GTIG) issued an advisory on a campaign targeting Salesforce instances.
The threat actor, UNC6395, used stolen OAuth tokens from the Salesloft Drift app to access Salesforce organizations, export data, and hunt for high-value secrets like AWS keys and Snowflake tokens. Because this was a classic abuse of non-human identities (NHIs), traditional security controls like MFA were completely bypassed.
In this quick response, we’ll break down:
- What happened in the attack.
- Why this is a critical wake-up call for NHI security.
- Actionable recommendations for what to do now.
What happened: Campaign rundown
According to the GTIG advisory, the data-theft campaign ran from August 8–18, 2025. Here’s a summary of the attack:
- Attack Vector: The threat actor, UNC6395, gained access using compromised OAuth tokens tied to the Salesloft Drift third-party application.
- Execution: They systematically exported large volumes of data from corporate Salesforce instances. Their primary goal was credential harvesting—searching the exfiltrated data for secrets like AWS access keys and Snowflake tokens to use in follow-on attacks.
- Evasion: The actor attempted to cover their tracks by deleting query jobs, but GTIG confirms that the relevant Salesforce logs remain intact for investigation.
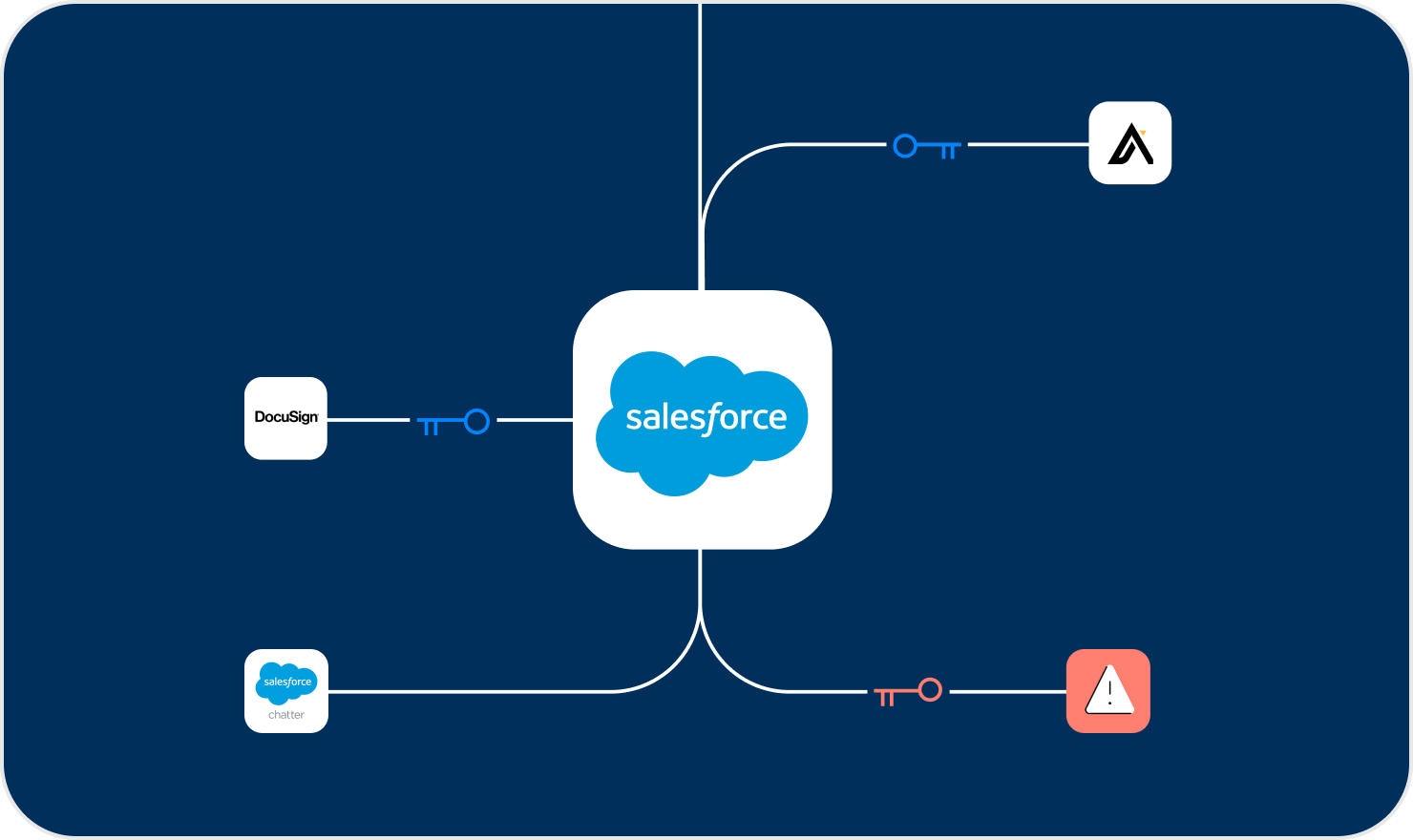
- Response: On August 20, Salesloft and Salesforce revoked all Drift access tokens. Salesforce has also removed the Drift application from its AppExchange pending further investigation. GTIG notes this was not a vulnerability in the core Salesforce platform itself.
The NHI attack vector explained
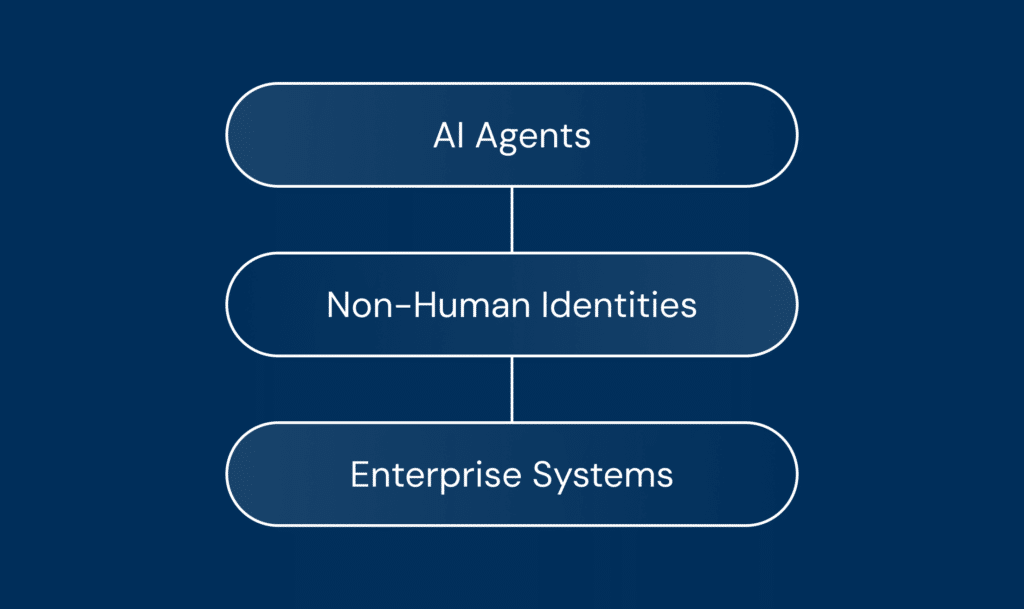
At its core, this attack abused non-human identities (NHIs)—the OAuth tokens and API credentials that connect applications.
Once the tokens were stolen, the threat actor operated silently, without needing to bypass MFA or interact with a user. This gave them a direct, trusted path to exfiltrate data and hunt for even more high-value NHIs, such as cloud infrastructure keys. The GTIG advisory specifically calls this out, urging customers to check for GCP service-account keys stored within Salesforce objects—another major NHI risk.
Threat actors now actively target NHIs because they are persistent, often have high-level privileges, and are deeply integrated across the modern enterprise stack. This campaign is a textbook example of that trend.
What to do now and how Astrix can help
The GTIG advisory is clear: “Organizations using Drift integrated with Salesforce should consider their Salesforce data compromised and are urged to take immediate remediation steps.”
Here are the immediate actions your security team should take:
- Review salesforce logs: Immediately review your Salesforce logs for any unusual queries or bulk data exports, especially between August 8–18, 2025.
- Revoke and rotate: Revoke any suspicious OAuth tokens associated with Salesloft Drift and other third-party applications. Implement a regular rotation policy for all credentials.
- Audit third-party integrations: Conduct a thorough audit of all third-party applications connected to your Salesforce instance. Enforce the principle of least privilege, ensuring that each application has only the permissions it absolutely needs to function.
- Hunt for exposed secrets: If you suspect you may have been a victim of this campaign, it’s critical to hunt for any leaked secrets within the potentially exfiltrated datasets.
- Talk to an Expert: The most important step you can take is to talk to an expert to help ensure all NHIs related to this incident are identified and secured. The Astrix team can help you gain visibility into your NHI landscape, identify and remediate risks, and implement a comprehensive NHI security program.
Secure your NHI attack surface
Navigating the aftermath of an incident like this is complex. Identifying every NHI related to this breach, validating logs for Indicators of Compromise, and hardening your overall security posture requires specialized expertise.
The Astrix team is here to help. We provide the visibility and control needed to secure your entire NHI landscape. If you use Drift with Salesforce or are concerned about your exposure from third-party integrations, talk to our team today. We’ll help you move fast to identify risk and secure your environment.