How to Discover & Remediate OpenClaw (MoltBot) Agents with Astrix
The emergence of OpenClaw (formerly MoltBot) has highlighted the danger lies in “Shadow AI” – autonomous agents deployed by employees on corporate endpoints without security oversight. Astrix customers were alerted to these risks in real-time as the OpenClaw situation unfolded.
In this blog we will show you how the Astrix platform has helped them to quickly detect and remove OpenClaw agents.
Check out our demo video to see how Astrix platform helps in real time
Since OpenClaw emerged, couple of weeks ago, we alerted Astrix customers about employees who had deployed OpenClaw on corporate endpoint devices – often with critical misconfigurations. In several cases, these setups could have enabled attackers to gain remote access to employee devices and establish persistent access to sensitive corporate systems such as Salesforce, GitHub, and Slack by leveraging exposed API keys, OAuth apps, cloud credentials, and other non-human identities (NHIs) granted to the agent.
OpenClaw Is Just the Tip of the Iceberg – While OpenClaw is just one example of an agent that can pose a serious risk, there are many other autonomous agents operating in the shadows with access to sensitive systems that IT and security teams may not even be aware of.
Step-by-Step Guide: Managing OpenClaw Risk in the Astrix Platform
The following guide demonstrates how the Astrix platform enables you to discover, investigate, and remediate OpenClaw risks based on the product workflow:
1. Instant Discovery via Risk Controls
The process starts at the Risk Overview dashboard, where Astrix surfaces the most critical threats.
- What you see: A dedicated “OpenClaw agents” high-priority alert appears under Top Findings.
- The Value: You get immediate, automated notification of the threat’s presence without manual searching.

Pressing on the alert takes you to the next screen, the AI Agents Inventory.
2. Unmasking the “Shadow” Agent
The AI Agents Inventory provides a transparent look at every agent running in your environment.
- What you see: A filtered list of OpenClaw instances, mapped to specific physical devices (e.g., DEV-LAPTOP-107) and their human owners (e.g., Dave Olive).
- The Value: Instead of chasing logs, you get a clear map of the agent’s footprint, significantly reducing the time it takes to identify the source of the risk.

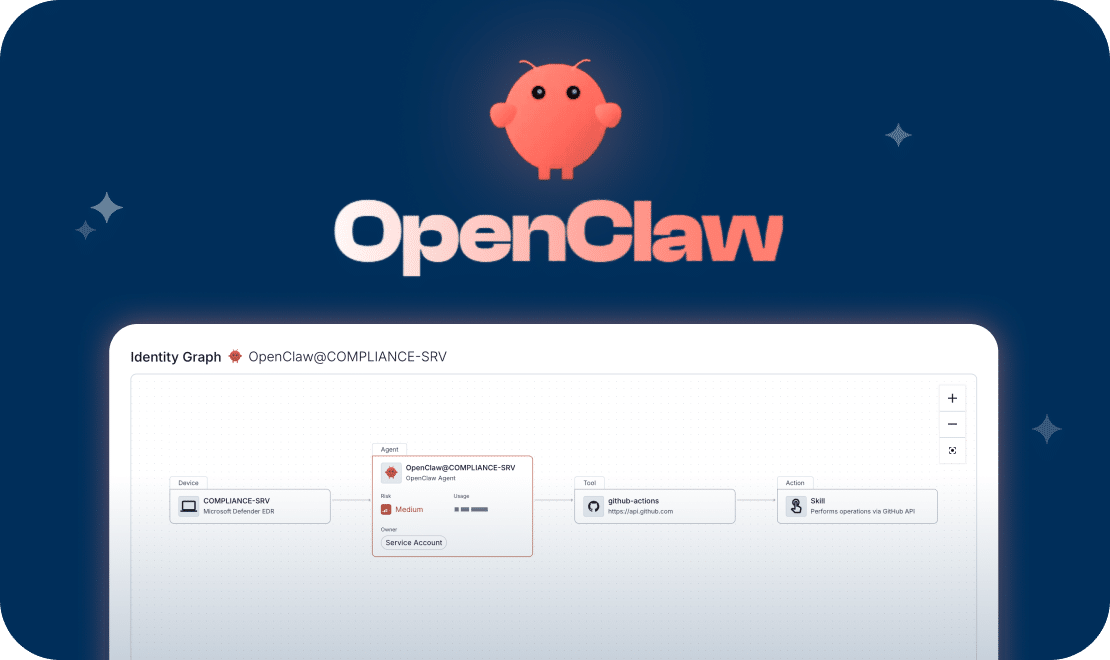
3. Visualizing the Blast Radius (Identity Graph)
To manage risk, you need to see exactly what the agent has the power to do.
- What you see: The Identity Graph visualizes the connection between the agent, tools and actions, and the end-user it is installed on.
- In addition: The sidebar shows the source, such as existing telemetry from your EDR (e.g., CrowdStrike or Microsoft Defender).
- The Value: You can investigate the agent and better understand its potential risks.
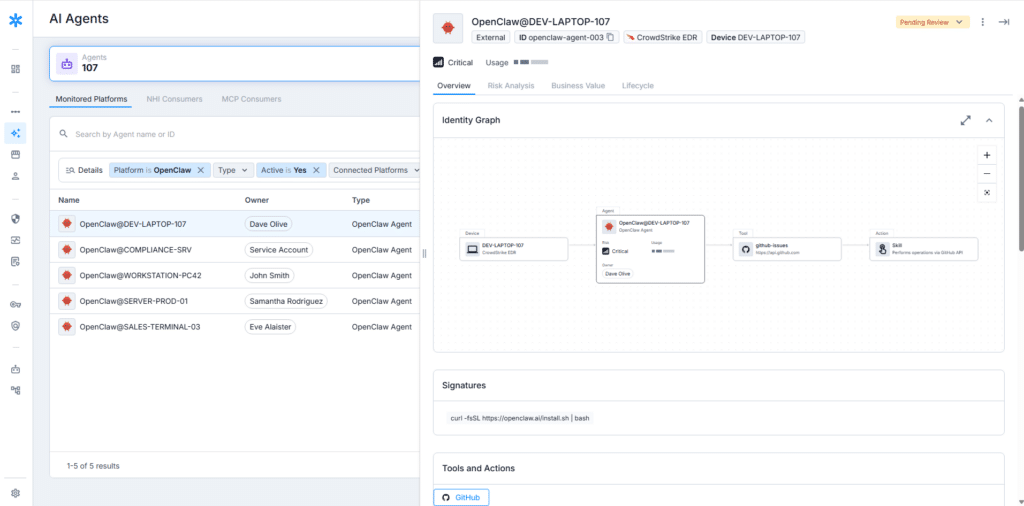
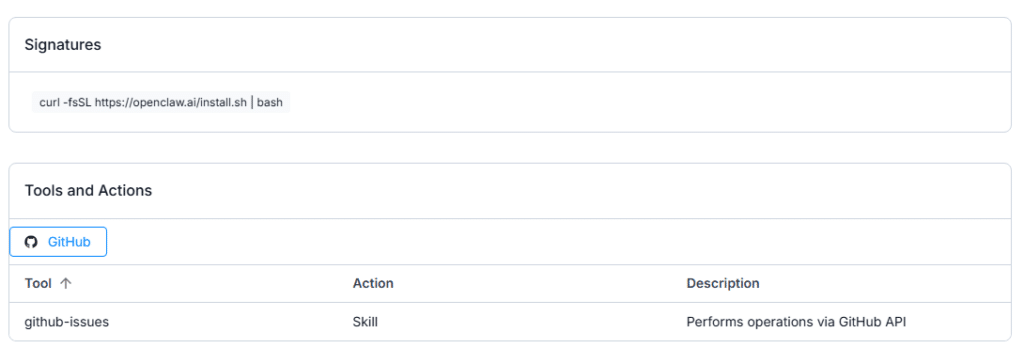
4. Forensic Proof with Signatures
For security teams requiring technical validation, Astrix provides the underlying forensic data.
- What you see: The Signatures section reveals the exact command line used to deploy the agent on the endpoint.
- The Value: This provides clear, factual evidence of the agent’s activity. Having this level of detail gives security teams a solid foundation when reaching out to the owner, allowing for a collaborative and transparent discussion about the installation and its risks.
5. Automated Remediation & Governance
Astrix allows you to move from discovery to action within a single interface.
- What you see: Through the Actions menu, you can mark agents as approved/unapproved, open tickets in your ITSM (like Jira), or trigger instant isolation via webhooks.
- The Value: You can also use the “Contact Owner” feature to automatically verify the business need with the employee, closing the security gap in minutes.

Our platform provides the necessary visibility to identify these autonomous agents across the organization and mitigate the risk before it escalates.
With Astrix, you don’t need to ban AI – you can govern it by instantly detecting and managing unauthorized agents that bypass traditional security layers.
While OpenClaw is just one example of an agent that can pose a serious risk, there are many other autonomous agents operating in the shadows with access to sensitive systems that IT and security teams may not even be aware of. To prevent similar incidents before they occur and reduce your overall attack surface, check out how the Astrix platform helped our customer identify and remove this threat on day one of publication –