Machine Credentials
WHAT are Machine Credentials?
Machine Credentials are a collective noun for Non-human Identities that operate as digital access keys used by systems. They are used to authenticate and communicate securely with other applications or services in the organization’s environment. By verifying a machine’s unique identity, machine credentials allow safe, agreed-upon interaction. Machine credentials come in various forms, including API keys, OAuth tokens, service accounts, and other certificates.
WHY Is It Important to Secure Your Machine Credentials?
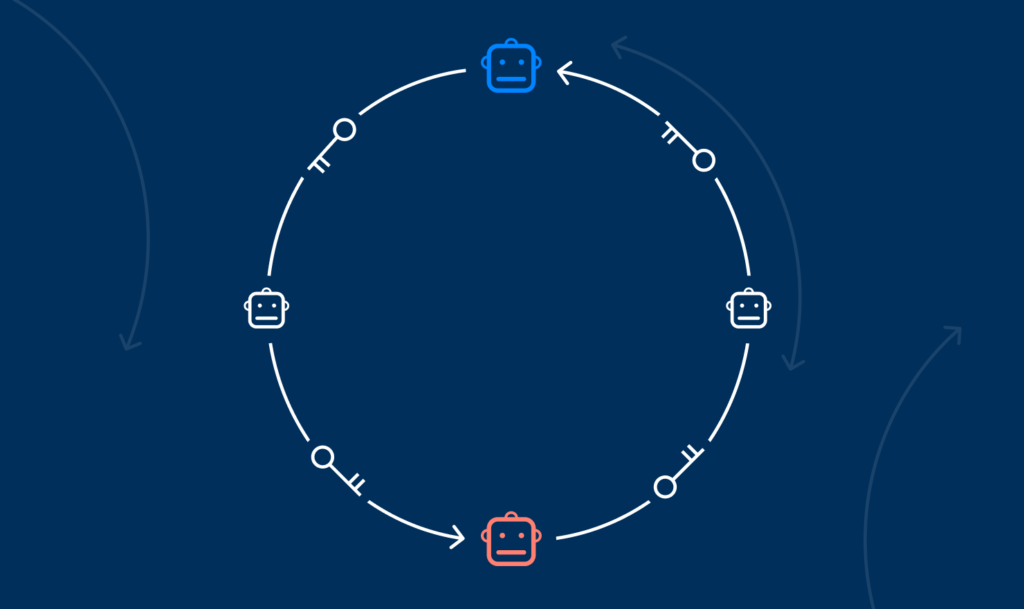
Machine Credentials are crucial to monitor and secure as they are widely used. They can be exploited as attack paths: from entry points, giving attackers initial access, to privilege escalation, lateral movement across the environment, persistent access, and backdoors.
Compared to human identities, which are typically managed under strict security protocols, organizations often overlook and neglect machine credentials. Machine credentials are usually overly permissive (giving excessive privileges beyond what is necessary for their purposes), easily granted, and aren’t adequately managed. This creates a significant attack surface and attractive targets for threat actors.
In a recent hack using machine credentials, cloud network Cloudflare was breached via a support ticket of its integrated system Okta (IT management service) using a compromised service account. Once inside the system, the attackers stole HAR files uploaded by Okta’s customers containing customers’ credentials. This is merely one example of a prevalent dangerous trend.
Even if your organization’s machine credentials are safe, the machine credentials of a third-party system or a non-native app integrated into your environment can be compromised and exploited. This is why it’s vital to use comprehensive, secure management of machine credentials in your entire organization’s environment.
HOW Can You Secure Your Machine Credentials?
To protect your organization from machine credentials-related risks, you must employ the following practices:
–Inventory: Build and manage a comprehensive and up-to-date inventory of all machine credentials used across your organization’s environments.
–Access management: Implement strict access standards, such as “least privilege” and regular credential rotation principles, to mitigate compromised credentials’ impact and “blast radius”.
–Monitoring: Monitor continuously the usage and status of machine credentials around your environments to detect and respond to changes and anomalies indicating a threat.
–Third-party risk management: Identify risks created by unsafe machine credentials of external third-party or non-native apps or services operating in your environment (i.e., Okta machine credentials integrating with Cloudflare, being the vulnerability).
–Incident response: Develop robust incident response plans and procedures to quickly detect, contain, and remediate any incidents involving machine credentials.
Astrix was built to help organizations close the security gaps created by machine credentials. It automatically compiles an inventory of Machine credentials across your organization and identifies overprivileged, redundant, or malevolent access. This helps uncover and address vulnerabilities without hurting your organization’s performance.