CSA and Astrix Research: The State of Non-Human Identity Security
As NHI attacks soar, CSA and Astrix reveal critical gaps in NHI protection. New data shows that one in five organizations have experienced a security incident related to non-human identities; and only 15% remain confident in their ability to secure them.
Findings from the State of Non-Human Identity Security Survey Report, a survey of more than 800 experts coupled with data from more than 2 million monitored NHIs in Fortune 500 companies, reveal a significant security disparity: organizations are far less equipped to secure non-human identities compared to their human counterparts. The most common challenges include service account management and NHI discovery. Though the survey also revealed there is a growing recognition of the importance of investing in NHI security with 1 in 4 organizations already investing in these capabilities and an additional 60% planning to within the next twelve months.
Download the full report here
"NHIs – like bots, API keys, service accounts, OAuth tokens, and secrets – are all lifelines of today’s organizations, enabling automation, efficiency, and innovation," said John Yeoh, Global VP of Research at CSA. "And while organizations recognize the importance of securing NHIs and often deploy a mix of tools like Identity Access Management systems, these tools are not specifically tailored to the unique challenges that NHIs present. The mismatch is evident in recent attacks on major brands like AWS, Okta, Cloudflare, and Microsoft, where despite having security measures in place, hackers still managed to infiltrate. This joint survey only underscores this vast issue, highlighting that NHIs can not be treated the same as human identities.”
Download the full report here
CSA and Astrix set out to dive deeper into how organizations perceive and handle NHI security, aiming to uncover the specific gaps and pain points in securing API keys, OAuth tokens, and more.
Key findings:
NHI attacks are surging and defenses are lagging

Nearly 1 in 5 organizations have experienced a security incident related to NHIs. The most common causes of NHI-related attacks were: lack of credential rotation (45%); inadequate monitoring and logging (37%); and over privileged accounts/identities (37%).
Low confidence in securing NHIs compared to human identities

There is a significant gap in organizations' security methods with only 1.5 out of 10 organizations highly confident in their ability to secure NHIs, compared to nearly 1 in 4 for securing human identities. This lack of confidence in securing NHIs versus human identities could be due to the sheer volume of NHIs in their environment, which often outnumber human identities by a factor of 20 to 1.
Fragmented approaches lead to security incidents
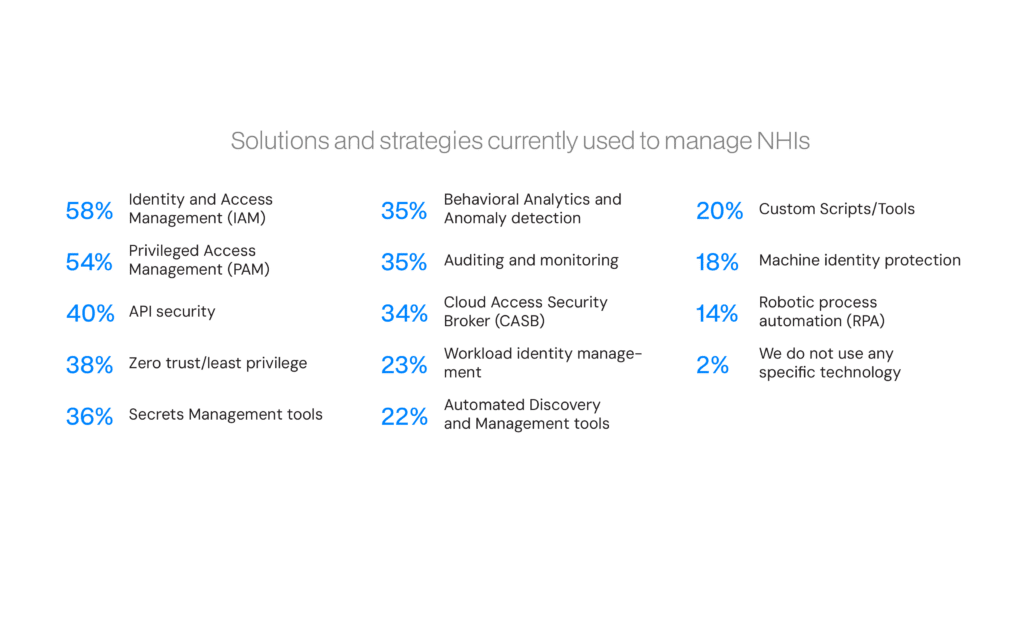
These tools are not specifically designed to address NHI security challenges; for instance: 58% use Identity and Access Management (IAM) systems; 54% use Privileged Access Management (PAM); 40% use API security measures; 38% employ Zero Trust/least privilege strategies; 36% use Secrets Management tools. As a result, the three most common causes of NHI security incidents include lack of credential rotation (45%), inadequate monitoring and logging (37%), and over-privileged accounts or identities (37%).
Struggling with fundamental security practices related to NHIs

Major challenges that organizations encounter include auditing and monitoring (25%); access and privileges (25%); discovering NHIs (24%); and policy reinforcement (21%). Another significant concern is the struggle to gain visibility into third-party vendors connected by OAuth apps, with 38% of organizations reporting no or low visibility into third-party vendors, and another 47% having only partial visibility.
Download the full report here




































