Astrix Security mentioned in a 2023 Gartner® report under Secure Access to Machine and Environments tool

In a recent Gartner report titled How to Select DevSecOps Tools for Secure Software Delivery, Astrix Security is mentioned as one of the vendors that addresses the need to secure access to machines and environments in the DevOps pipeline. In this short article we will cover key points from the report, and explain how Astrix solves the non-human access problem.
With the benefits of the growing use of quick and agile development practices, open-source resources and cloud-native architectures, security and compliance risks also increase and expand to new, often unknown realms.
According to the report, “Software supply chain attacks have added a new dimension to software security problems because the software delivery pipelines and the tools used to build and deploy software are the new attack vectors.”
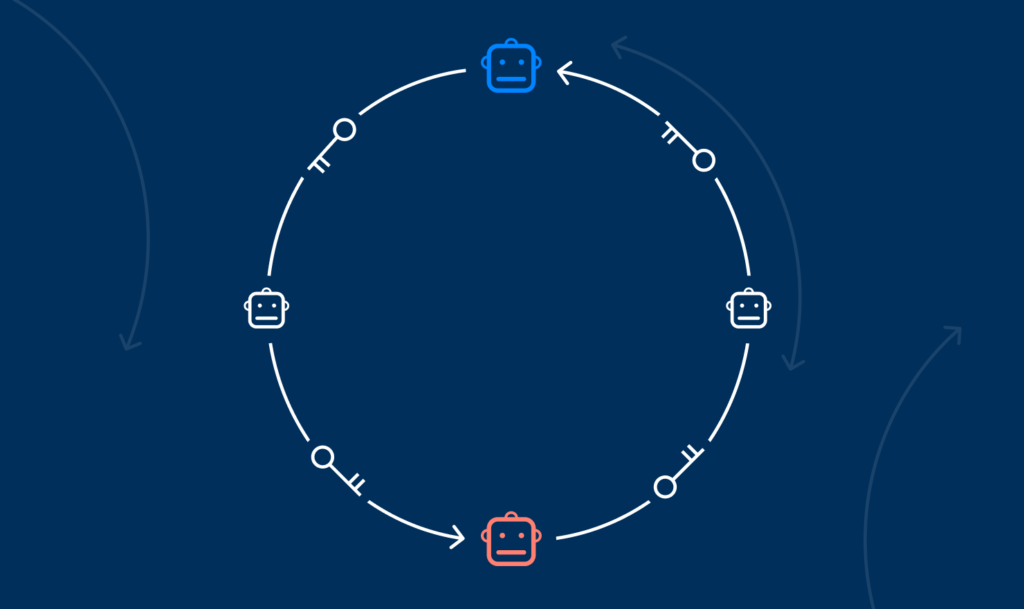
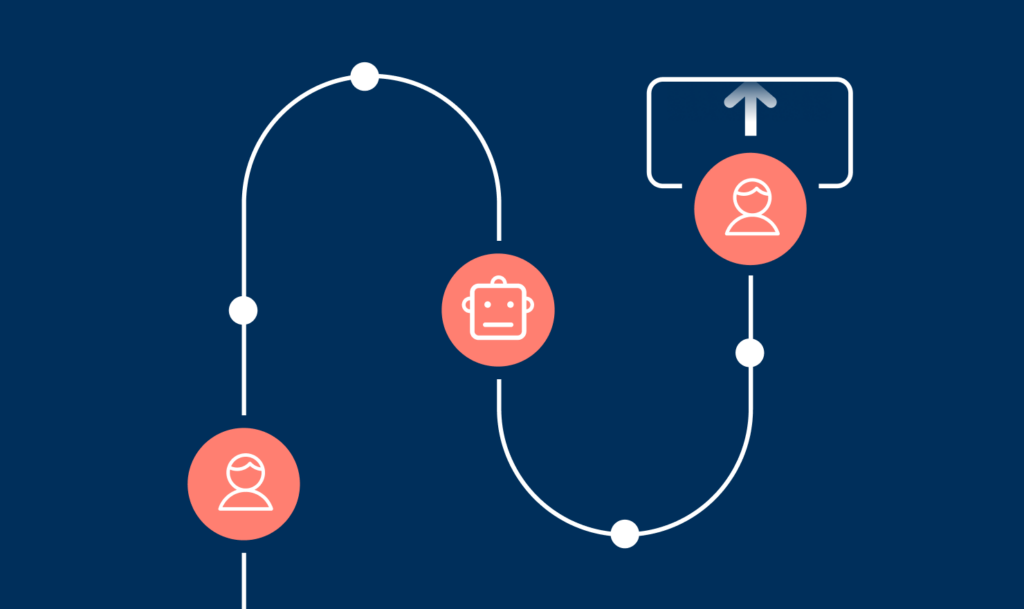
While the software supply chain has been a huge catalyst for vulnerabilities, and consequently attacks, a new type of supply chain attacks has proliferated in the past year – taking advantage of the third-party tools and services that are connected to these development environments. These are service supply chain attacks, in which attackers take advantage of access granted to third-party cloud services as a backdoor into the companies’ most sensitive core systems.
In the report, Gartner analysts recommend to engineering leaders that “In addition to securing software, they should also secure access to machines and environments and take an integrated security approach that extends to production.”
In search of productivity and automation, engineering teams freely adopt third party services on a regular basis through tokens, SSH keys, apps marketplaces and low codeno code platforms – more often than not with no governance of the security team. This leaves these highly sensitive development environments exposed to service supply chain attacks, just like the recent GitHub and CircleCI breaches.
Astrix helps engineering teams secure these non-human (machine) access to development core systems like GitHub and BigQuery, by providing a consolidated and comprehensive view of all the internal and third-party integrations to engineering environments (repositories, workflows, and configurations). Additionally, Astrix automatically identifies malicious third-party connections, anomalous behavior (like suspicious source IPs), overly permissive connections, redundant applications, and insecure tokens.
By automating remediation workflows, integrating with daily IT service management tools, and enabling end-users to resolve security issues in the process, Astrix can automatically remediate development core systems security risks, which helps take the burden off of IT and security teams, and helps engineering teams with ensuring their development environments are safe.
Astrix already helps cloud-first companies such as Figma, Exabeam, Pagaya and Bloomreach to safely unleash the power of app-to-app integration and automation. Schedule a live demo to see how it works.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Gartner does not endorse any vendor, product or service depicted in its research publications and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.