Salesforce Revokes Gainsight App Tokens: Latest OAuth Supply Chain Breach
November 22, 2025 update:
Salesforce publishes IOCs for Gainsight breach
Salesforce has published a list of Indicators of Compromise (IOCs) regarding unauthorized access to customer data through compromised Gainsight applications. Get the full list here.
Additionally, our research now investigates the threat actor’s attack pattern across three distinct phases:
Phase 1 – Reconnaissance (October 23rd): Initial token validation testing via AWS Lambda from IP 3.239.45.43 using user agent python/3.11 aiohttp/3.13.1.
Phase 2 – Testing (November 16-18th): Preliminary data exfiltration attempts from proxy IPs using python-requests/X.X.X user agent.
Phase 3 – Mass Exfiltration (November 18-19th): Large-scale data extraction using a batch tool with the distinctive user agent Salesforce-Multi-Org-Fetcher/1.0 from multiple VPN/proxy IPs.
Salesforce has issued a security advisory regarding unusual activity involving Gainsight applications connected to Salesforce. Threat actors have compromised third-party OAuth tokens to gain unauthorized access to Salesforce customer instances. In response, Salesforce and other major SaaS vendors have revoked all active access and refresh tokens for Gainsight-published apps and temporarily pulled those apps from the AppExchange while the investigation continues. Impacted customers have been notified directly.
In this quick response, we’ll break down:
- What happened and why we view this as a recurring threat pattern
- Additional details and context from the Astrix Research Team
- Actionable recommendations for what you can (and should!) do now
What happened
On November 20, 2025, Salesforce issued a security advisory announcing the detection of an “unusual activity” involving Gainsight applications installed in customer environments. The investigation revealed that threat actors compromised the OAuth tokens (Non-Human Identities) connecting Gainsight to Salesforce.
The prolific hacking group ShinyHunters has claimed responsibility for the breach to DataBreaches.net and BleepingComputer. Per reports, ShinyHunters claim to have accessed roughly 285 additional Salesforce instances after breaching Gainsight with secrets stolen in the earlier Salesloft Drift incident; Gainsight previously confirmed it was compromised via stolen OAuth tokens.
Upon detection, Salesforce took immediate containment actions:
- Revoking all active access and refresh tokens associated with the affected Gainsight applications.
- Temporarily removing the applications from the Salesforce AppExchange.
- Directly notifying affected customers.
Following the initial disclosure, Gainsight provided further updates regarding their response to the incident. The company has engaged Mandiant to support the ongoing forensic investigation and, as a precautionary measure, has also disabled their Zendesk application alongside the Salesforce integrations. According to Gainsight’s internal analysis, the scope of the compromise is currently believed to be limited to the “Gainsight CS” product, affecting three organizations, all of which have already been contacted by Salesforce. Gainsight further stated that no other integrations appear to be compromised and that they are making lists of suspicious IP addresses available to customers via direct support ticket requests.
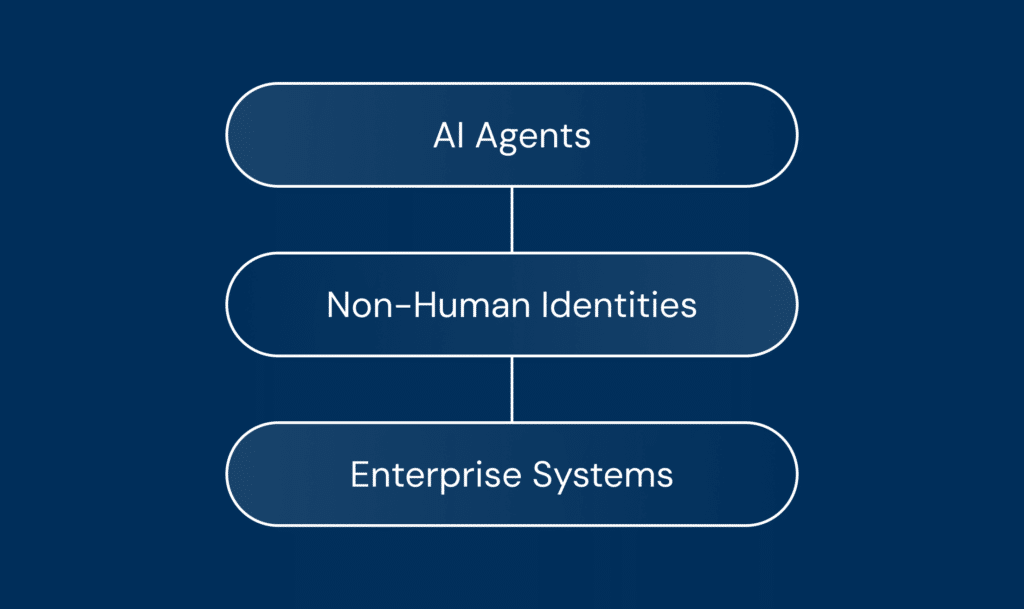
A recurring threat pattern: NHI attack vector
This incident mirrors the recent Salesloft Drift breach that happened back in August. We are witnessing a clear, escalating pattern where adversaries are bypassing traditional perimeter defenses by targeting app-to-app connections.
In modern environments, third-party integrations are granted persistent, high-privileged access via OAuth tokens. These non-human identities often go unmonitored. If an attacker compromises the third-party vendor (in this case, the integration tokens), they inherit those privileges, allowing them to access, exfiltrate, or manipulate customer data without ever touching a user password.
What to do now and how Astrix can help
The immediate response step we recommend is to revoke and rotate all tokens and secrets that were shared with Gainsight. The problem: Gainsight connects into many systems (Salesforce, Slack, Entra ID, Google Workspace, browsers and more). These integrations are often owned by different teams and were set up years ago. That makes it nearly impossible to be confident you have revoked everything.
As a starting point, search your environment for the following Gainsight identifiers (this list is not exhaustive, but it will help you find some of the key integrations fast):
- Slack app IDs: A5FKXF3EV, ACUQBEDTL, AJHA60Q5C, A06MHS5K0SG
- Entra ID application IDs: 6cd07c04-af3e-4917-b505-32a49a792f7c, 5be4377f-a2de-423d-b433-c9ce8016eb92
- Google Workspace OAuth client IDs: 982040983797, 674556516982, 909983063050
- Chrome extension ID: kbiepllbcbandmpckhoejbgcaddcpbno
From there, here are the immediate actions your security team should take:
- Revoke and rotate Gainsight credentials: Confirm that all Gainsight-connected app tokens are revoked in Salesforce (Connected Apps OAuth Usage) and that related integration users are disabled or locked down. Rotate any remaining credentials that were shared with Gainsight.
- Audit third-party integrations: Conduct a thorough audit of all third-party applications connected to your Salesforce instance. Enforce the principle of least privilege, ensuring that each application has only the permissions it absolutely needs to function. Attackers often create “backdoor” integrations to maintain access after the initial token is revoked.
- Review Data Access Logs: Analyze Salesforce event logs for anomalous data export activities or bulk API calls initiated by the Gainsight integration user prior to the revocation.
- Assume data exposure and rotate secrets: If Gainsight had access to support cases, notes, or attachments, assume any credentials stored there may now be exposed. Rotate relevant keys, tokens, and passwords.
- Monitor Official Channels: Keep a close watch on status.salesforce.com and https://status.gainsight.com/ for further patch instructions or indicators of compromise (IOCs).
- Talk to an Expert: The most important step you can take is to talk to an expert to help ensure all NHIs related to this incident are identified and secured.
Both Gainsight and Salesloft incidents highlight the critical need for visibility into your Non-Human Identity (NHI) landscape. You cannot secure connections you cannot see.
The Astrix team is here to help. We enable you to quickly gain visibility into the NHI landscape, identify and remediate risks, and implement a comprehensive NHI security program. If you are concerned about your exposure to this incident or want to audit your third-party integrations, contact the Astrix team for an immediate assessment.
We’ll help you move fast to identify risk and secure your environment.