Built Different:
A Unified Threat Center for AI Agent Security
If you’re in the security space today, there is a good chance your AI agents and non-human identities (NHI) are already doing a lot behind the scenes. Authenticating, pulling data, calling APIs, and chaining tools together. Most of that activity is not meaningfully visible or understandable in your existing security tools.
Conversations with security teams reveal a consistent pattern. They know AI agents and NHIs are everywhere, but they are mostly blind to how those identities behave day to day.
When they do start turning on deeper logging or deploy a platform that exposes non-human identity activity, a new problem appears. The manageable trickle of events turns into a stream of alerts that is hard to prioritize and hard to own.
From blind spots to alert avalanche
Most organizations face a fundamental challenge: non-human identities and AI agents operate across every environment, yet they’re rarely treated as first-class identities in security programs. Their activities are buried in generic logs or not logged at all. Existing detections focus on human users, not automated workflows.
Once you gain visibility into NHI activity, a second problem emerges immediately: alert overload. Signals land everywhere, fragmented across multiple tools with no unified context. A service account accessing 10,000 files might be normal for one agent and wildly suspicious for another. An OAuth token making API calls from a new country could be legitimate automation or credential theft. Without context specific to non-human identity behavior, every alert becomes a research project.
The cost is measurable. Critical threats get lost in the noise. Alert fatigue sets in. Response times creep up. Organizations that deploy AI agents for velocity often end up moving more slowly because security can’t confidently determine what’s safe.
What’s needed isn’t more alerts, it’s intelligence that delivers visibility, context, and clear remediation guidance.
Turning fragmentation into intelligence
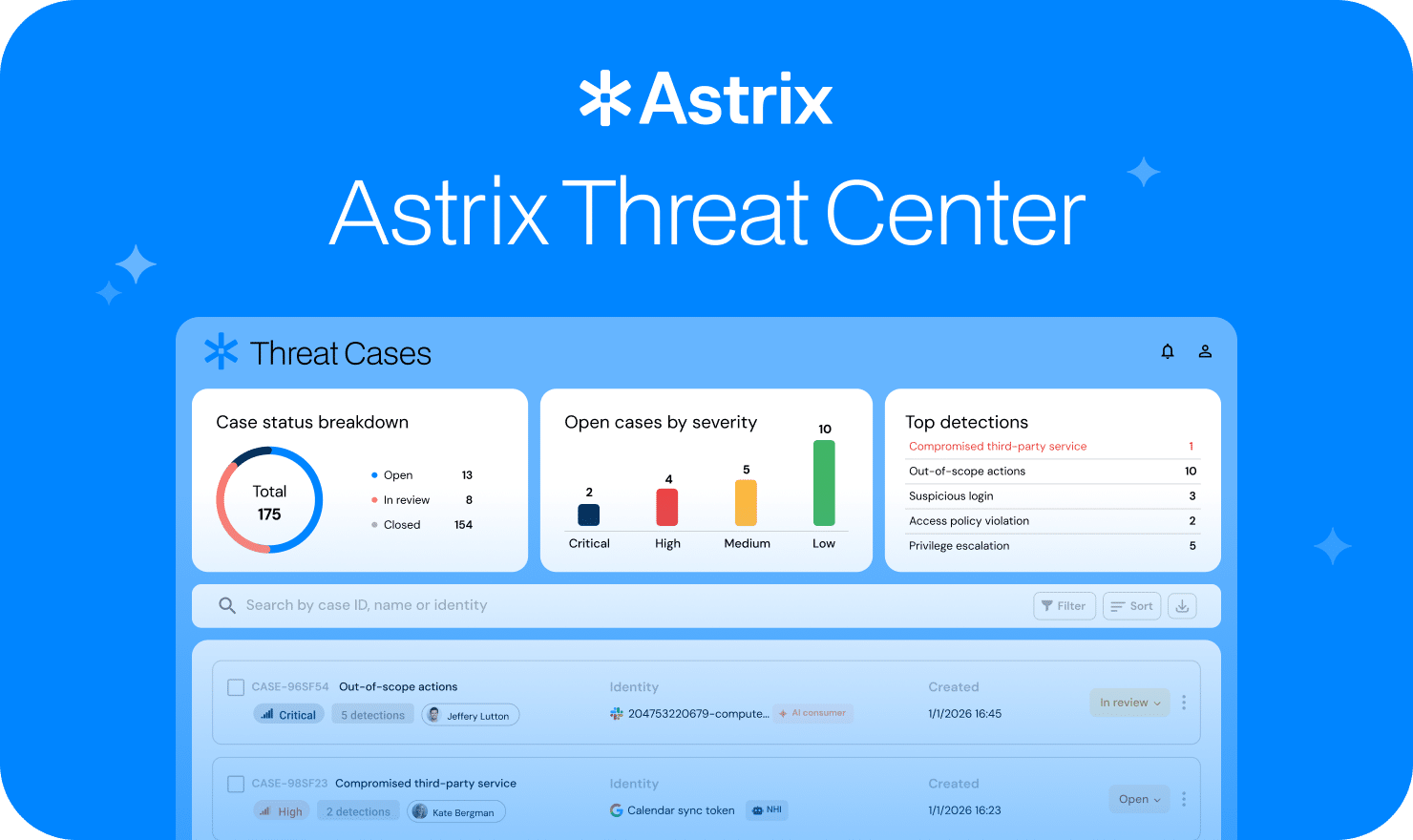
This is where Astrix’s Threat Center, a centralized hub for triaging, investigating, and managing threats surfaced by Astrix’s threat detection engines, comes in. This represents a fundamental shift in how organizations should approach AI agent and non-human identity security.
The core insight: security teams need intelligence that’s unified, prioritized, and actionable. Rather than surfacing every individual detection event, Astrix aggregates related signals into unified “Threat Cases” that tell a complete story.
Think of it this way: if five different detection engines all flag suspicious behavior related to the same compromised OAuth token, you shouldn’t get five separate alerts. You should get one “Threat Case” that shows the full scope of the incident, affected entities, and guided next steps.
We’ve seen this make an immediate difference. What used to take hours of correlation work now surfaces automatically in minutes. The improved clarity meant analysts could handle investigations that previously required senior escalation.
Source: Astrix’s Threat Center dashboard
AI agents as first-class security citizens
Astrix Threat Center treats AI agents as what they are: a distinct class of identity requiring purpose-built detection and response, not just “users with weird behavior.”
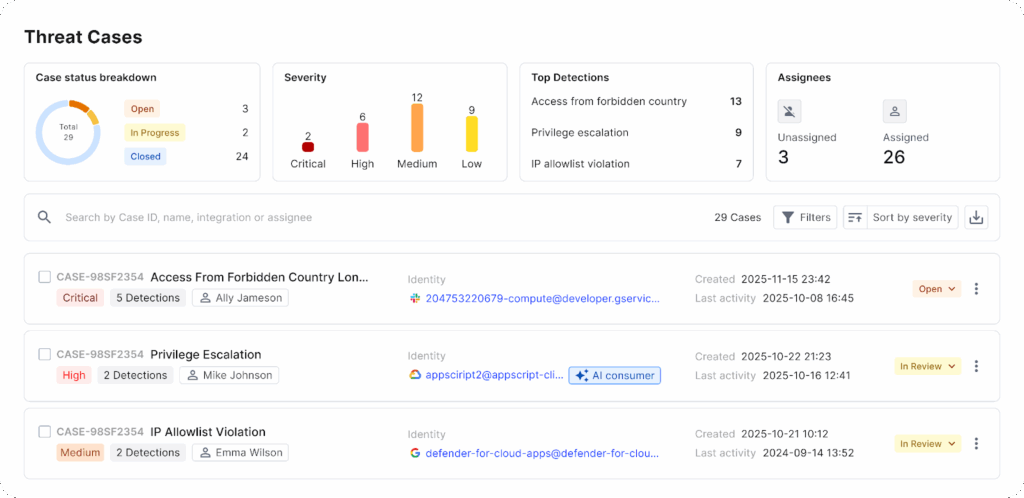
Our threat detection engines understand what’s normal for service accounts, OAuth applications, and API keys, spotting when agents access unexpected data or when patterns suggest credential compromise. We surface threats broader platforms miss entirely: policy violations, anomalous agentic workflows, supply chain risks and more.
However, detection alone isn’t enough. Each Threat Case delivers clear context about affected entities, scope, and remediation guidance. Built-in ticketing lets you assign, track, and collaborate without switching tools. Native webhooks and API support trigger automated playbooks in your existing SOAR platform, no manual handoffs required.
Fine-tuning to your reality
Every organization’s “normal” looks different. What’s suspicious in one environment might be routine in another. Generic detection rules can create false positives, eroding trust in the system.
That’s why Astrix Threat Center includes granular exclusions management. Security teams can fine-tune detections based on their organizational understanding, eliminating noise from expected behaviors while maintaining coverage of genuine threats. You can define custom access policies at the country and integration level, aligning Astrix’s detection engines with your actual security posture.
It’s the balance teams have been asking for: powerful detection without the overwhelming burden of false positives.
The path forward
Security teams don’t need more alerts, they need clarity. AI agents will continue to multiply, integrations will continue to expand, and noise will only grow unless detection becomes purpose-built for non-human identity behavior.
Astrix Threat Center closes that operational gap with unified Threat Cases, guided investigation, and automated response workflows that reduce MTTR and let teams stay ahead of incidents instead of chasing them.
Interested to see more? Visit us at https://astrix.security/ to learn more about AI agent and NHI security.





































