Security Magazine – Non-human identities: Secure them now, not later
Astrix CTO & Co-Founder Idan Gour shares his insights with Security Magazine about identity-related attacks being on the rise, with credential misuse becoming a prominent attack vector.
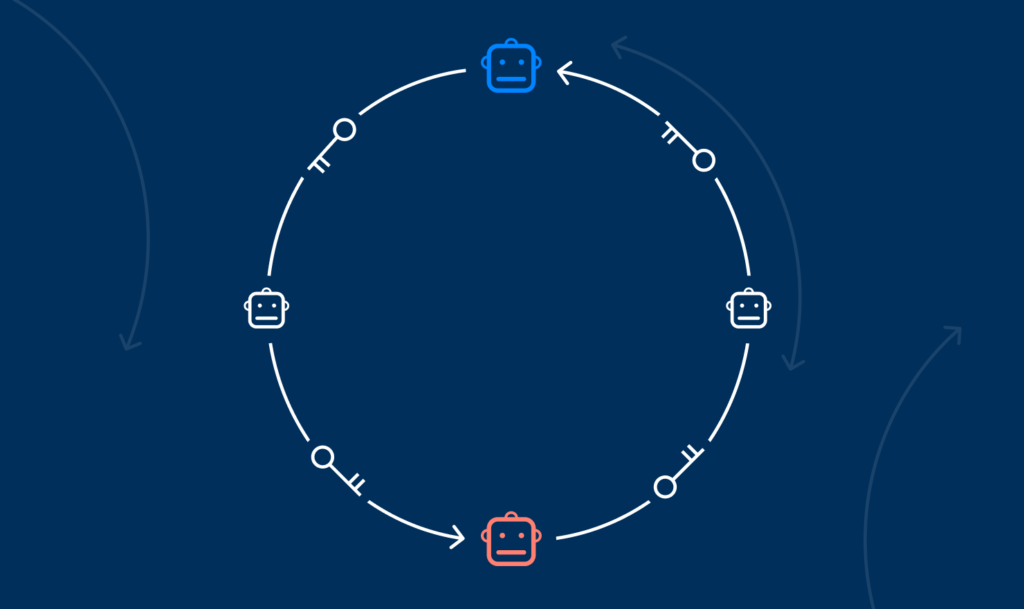
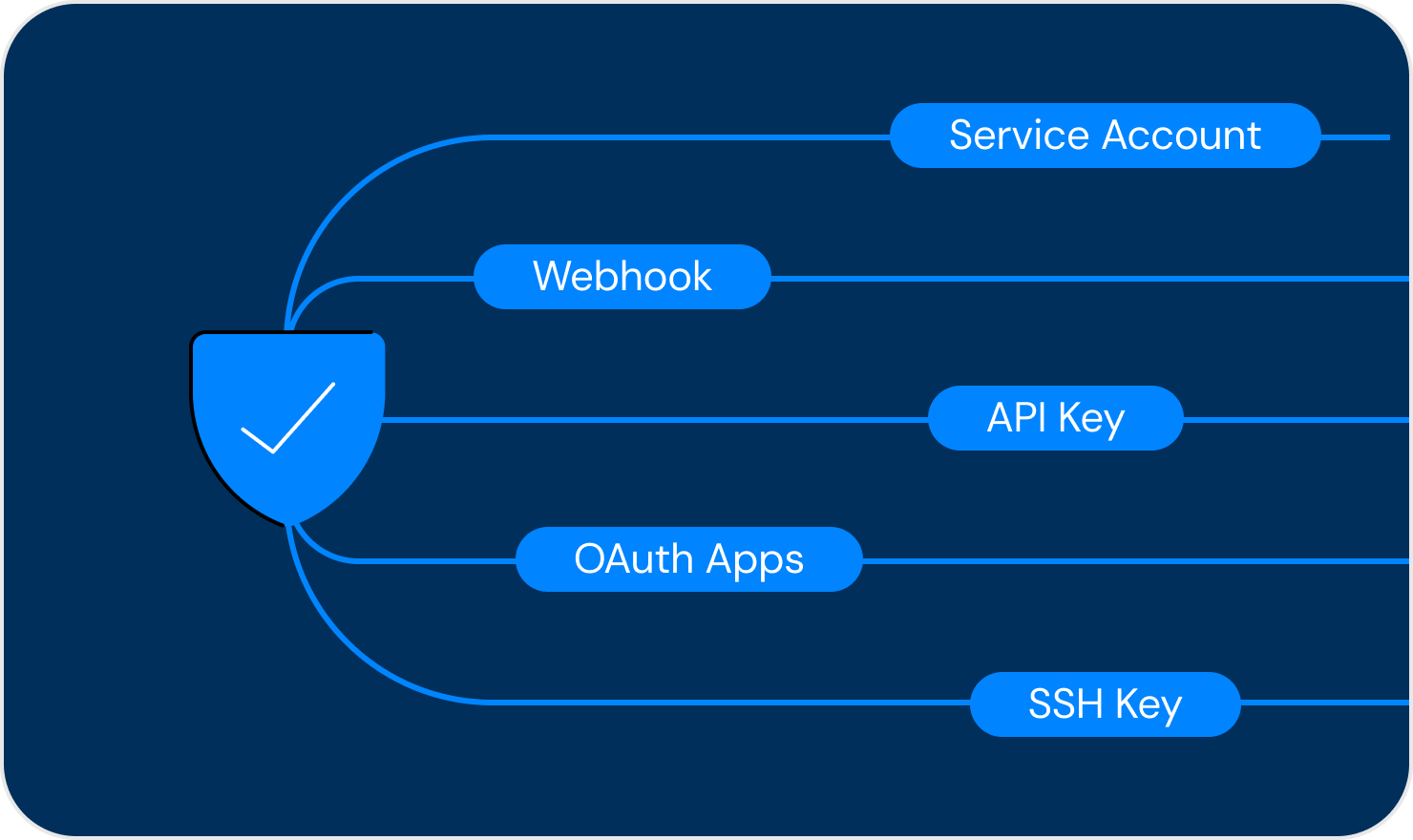
Recent high-profile incidents have highlighted the exploitation of insecure non-human identities, such as API keys and OAuth tokens, to breach organizational systems, steal sensitive data, and cause disruptions.
In the article, he covers:
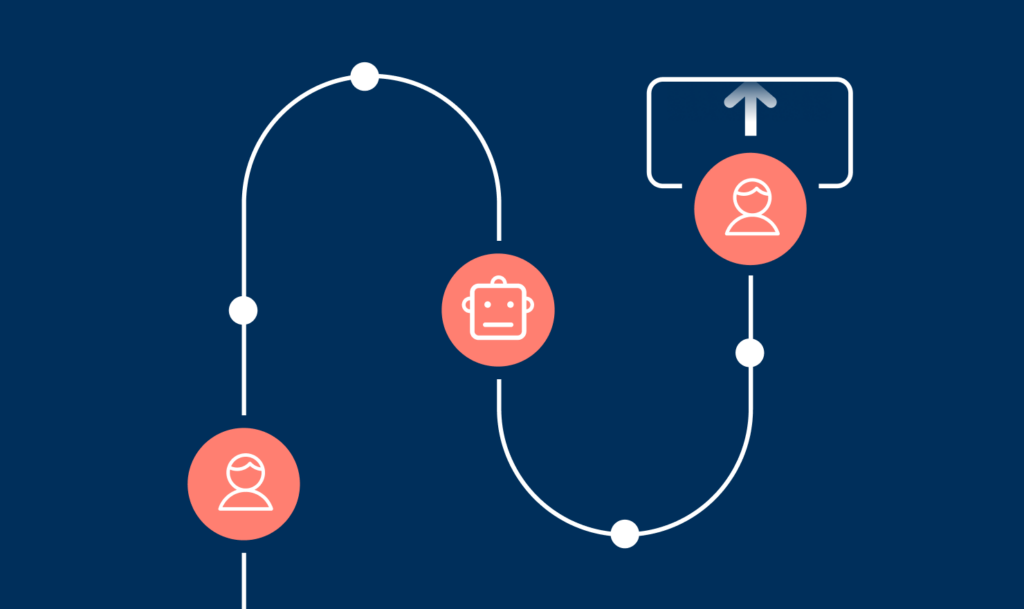
- Why identity-related attacks persist in the cybersecurity industry with three main types of threats: supply chain attacks, OAuth phishing, and company access token attacks.
- The importance of securing non-human identities and extending access management strategies beyond users.
- All about attacks targeting trusted vendors like GitHub, Microsoft, and Slack.