Agentic Threat Detection & Response
Leverage Astrix’s ML-based threat detection engine to identify suspicious activity involving AI agents, such as unusual access patterns, out-of-scope actions, IoCs, and exposed credentials.
AI Agent risks are not theoretical
80%
of companies reported AI agents taking unintended actions, incl. downloading sensitive content.
50%
said their org experienced a confirmed or suspected cyber incident caused by AI agents.
Astrix expedites MTTR for agent threats
Which OWASP agentic threats does Astrix defend against?
Based on OWASP Agentic AI Top 15 Threats report
T3 – Privileged Compromise
AI agents often operate with privileged credentials such as API keys, service accounts, or tokens. Whether maliciously exploited or unintentionally misused, these identities can give agents deep access to critical systems and data, turning any compromise into a high-impact event.
T2 – Tool Misuse
Agents connected to powerful tools can be manipulated or simply misconfigured to carry out unintended actions. This may include running unauthorized commands, modifying records, or triggering workflows that were never meant to run — causing harm with or without attacker involvement.
T9 – Identity Spoofing & Impersonation
Agents can impersonate trusted users or services, or be tricked into revealing sensitive credentials. These risks can stem from deliberate attacks or from poor identity handling by the agent itself, leading to unauthorized access across multiple systems.
T13 – Rogue Agents & Unchecked Autonomy
Autonomous agents act at machine speed and make unpredictable decisions. Even without compromise, their unchecked autonomy can create cascading issues across environments, escalating small missteps into enterprise-wide disruptions in seconds.
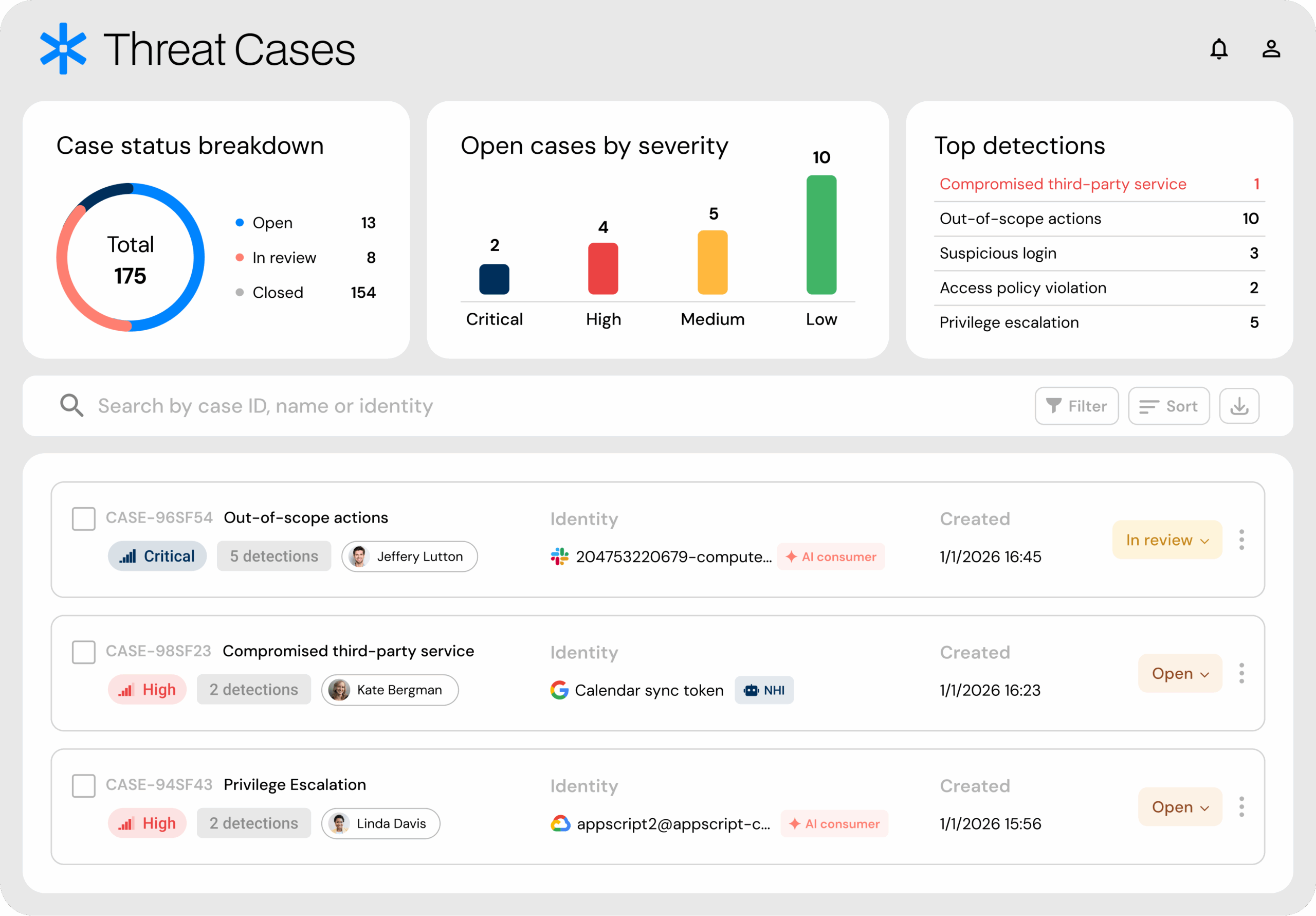
Threat Center
Unified Threat Detection & Response for AI Agents & NHIs
Central hub for detecting, triaging, and managing threats across AI agents and NHIs. Astrix Threat Center consolidates fragmented alerts into prioritized Threat Cases, reducing investigation time and closing security blind spots.
How it’s done
Real-time anomaly detection
SOC teams can focus on high-risk threats without being overwhelmed by noise. Astrix’s ML-based engines continuously analyze agent behavior across access patterns, IP addresses, permission changes, secret usage, and connected vendors. By establishing accurate behavioral baselines from both historical and near real-time data, Astrix quickly flags out-of-scope or suspicious activity while minimizing false positives.
Seamless integrations & guided remediation
SOC teams can leverage Astrix’s out-of-the-box workflows or integrate seamlessly with ITSM, SIEM, and SOAR platforms to design tailored remediation flows that align with their unique policies and threat landscape. With investigation guides and playbooks, teams can quickly investigate, respond, and mitigate risks before they escalate. Astrix also supports owner-assisted fixes — such as agent ownership assignment, permission reduction, or configuration changes — by engaging employees directly through collaboration tools like Slack.
Forensic visibility & audit trails
SOC teams gain the visibility and speed they need to investigate incidents and uncover root causes fast. Astrix captures every agent action with full context — human owners, non-human identities, permissions, credentials, usage patterns, and accessed resources. Embedded playbooks, investigation guides, and complete audit trails streamline analysis and enable effective, timely response.
Learn more
Ready to see Astrix in action?
See how Astrix can help you discover and remediate NHI risks across your environments.

































